Calliope Pro now offers security vulnerability scanning as a service feature.
We’ve combined several enterprise-level vulnerability scanning tools into one service to provide your organisation with a comprehensive assessment of its security vulnerabilities, delivered through Calliope Pro. This service delivers enterprise-level infrastructure and web application vulnerability scanning without paying enterprise-level prices, using BurpSuite, Nessus, and OWASP ZAP.
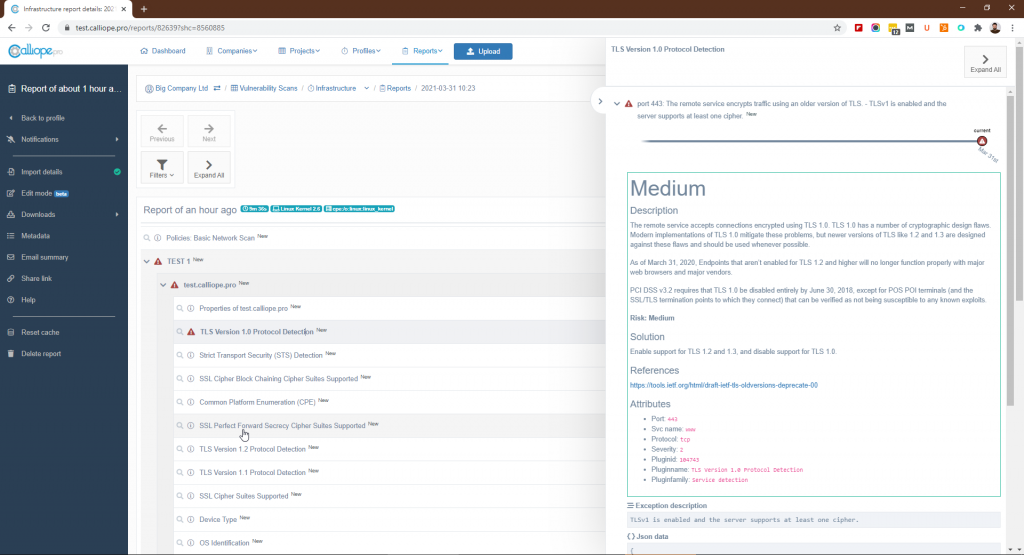
All these solutions are deployed in our own Google Cloud infrastructure for complete control over the runtime environment. The results of the security tests are available to customers in custom profiles in their Calliope Pro account. Results can be viewed in the standard Calliope Pro dashboards and reports, as well as downloadable PDF reports direct from the scanning tool



Setting up vulnerability scanning
Each paid account can have one IP or domain set up for security testing at no extra charge to you. If you have a free Starter Account you will need to upgrade or request vulnerability scanning separately. Should a customer desire more IPs or domains to be tested, we are able to configure this for you with pricing based on the number of IPs/Domains.
Security vulnerability scanning as a service requires some customer work upfront to get it configured and working. To get started setting this service, please use the form below to provide us with the name and phone number of a contact person and we will call you within 24 hours to get the ball rolling.
Why perform vulnerability scanning with Calliope Pro
Similar to bugs stemming from the normal development process, we see the identification and remediation of security issues as a quality issue that is found and fixed by the multidisciplinary software development team.
In this philosophy, automated vulnerability scanning and the results generated from them should be continuously monitored in much the same way that automated test results are – which is currently supported by Calliope Pro. Our ethos is to help development teams create high-quality applications, faster and cheaper. Security is an increasingly important indicator of high-quality software.
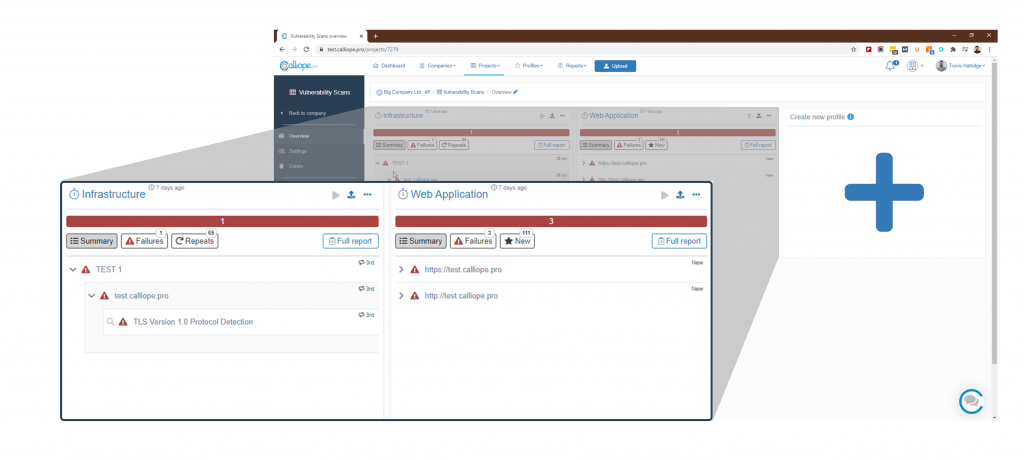
Dashboards for better organisation
As the SUT (System Under Test) grows, so does the number of components and environments being tested. This has the potential of turning hundreds of test results into an unorganised mess where the data you need for decision-making is hard to find.
Vulnerability scanning with Calliope Pro helps organise test results so the result of recent scans is at your dev team’s fingertips.
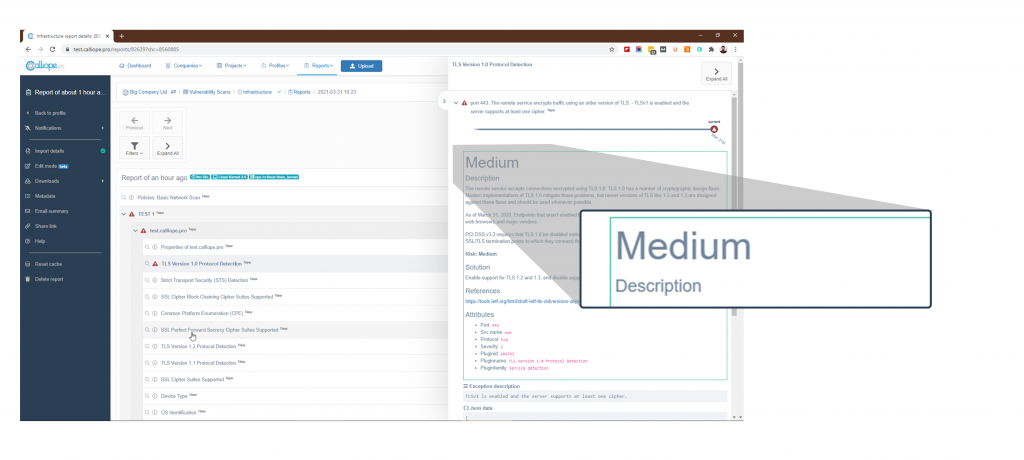
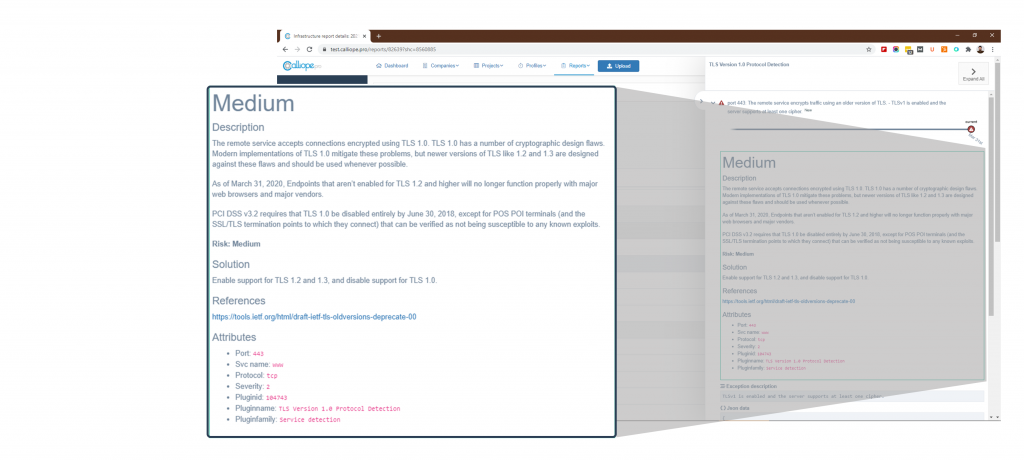
Prioritise on severity
Simply knowing there is a vulnerability is not enough, the dev team needs to know the severity of vulnerabilities to know where to prioritise their efforts.
Vulnerability scanning with Calliope Pro uses Nessus, BurpSuite and OWASP ZAPs professional database of CVE* to give you the most up-to-date information on which vulnerabilities require your immediate attention.
Daily, weekly, or
monthly scanning
Vulnerability scanning is often your first line of defense against security flaws and cybercrime. You can’t fix a problem if you don’t know it exists.
Vulnerability scanning with Calliope Pro provides your organisation with the flexibility to choose the frequency of vulnerability scans to fit your security policy and budget.
Immediate insight
into vulnerabilities
Using Calliope Pro’s advanced data visualisation features, you can get immediate insight into the results of the latest vulnerability scans.
See at a glance if there are new vulnerabilities found or a high number of critical vulnerabilities that need your immediate attention.
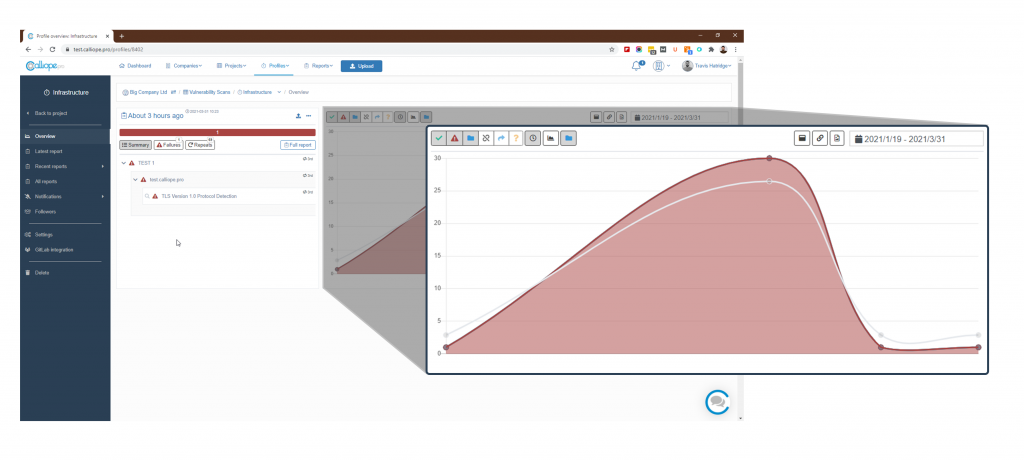
Track vulnerabilities
over time
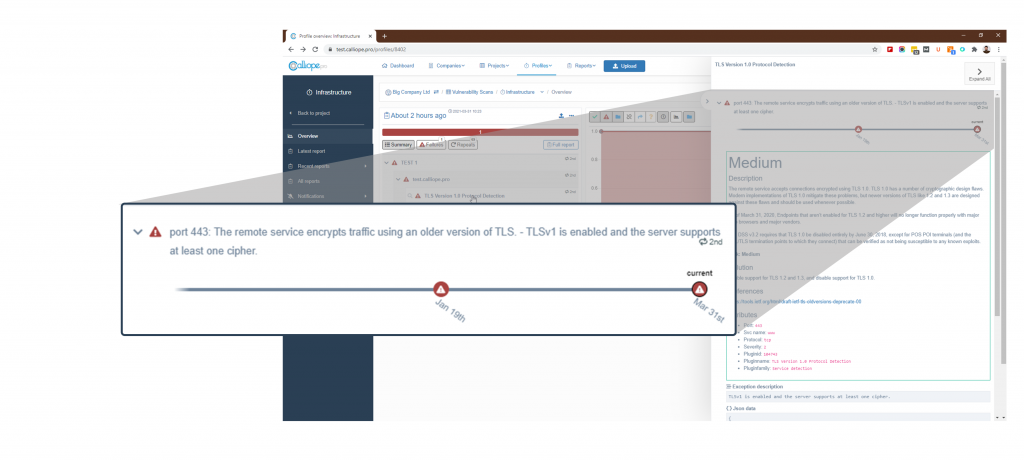
As your web applications and infrastructure develop over time, there is the chance that a vulnerability once fixed could once again become an issue.
Using vulnerability scanning with Calliope Pro gives your team the insights needed to correlate recent updates to new and past vulnerabilities using our timeline of scan results.
Penetration testing
at a discount
The ability to scan for vulnerabilities in a cost-effective and flexible manner is already incredibly important for the security of your organisation.
But what happens when you need to further cybersecurity testing?
With vulnerability scanning with Calliope Pro, you get discounts and priority status on our enterprise-level penetration testing services and our cybersecurity consulting.
Interested in guarding your apps and infrastructure?
Use the contact form to get in touch and we will set it up for you!
